Here are updated and valid dumps to pass VMware 2V0-21.19,2V0-41.19,3V0-624,3V0-752,5V0-21.19 exam. We have valid and updated VMware dumps,braindump questions updated 2020 https://www.pass4itsure.com/vmware.html Come learn!
100% Guarantee Download VMware 2V0-21.19 Exam PDF Q&A https://drive.google.com/open?id=1YIIK99ErOg-sWut8CpSDlvPLViJRXq0z
100% Guarantee Download VMware 2V0-41.19 Exam PDF Q&A https://drive.google.com/open?id=15OVNOX-4aLX8qJuvLhvo98SYR58sjjGs
100% Guarantee Download VMware 3V0-624 Exam PDF Q&A https://drive.google.com/open?id=1PnEplZLRf8m_9Tz-ohzSiH9iW616Lfn7
100% Guarantee Download VMware 3V0-752 Exam PDF Q&A https://drive.google.com/open?id=1T4Yzzeb0rA7SYuRg088XRsF7gD1xS2y_
100% Guarantee Download VMware 5V0-21.19 Exam PDF Q&A https://drive.google.com/open?id=1BkJENokCYD5FkYVqazpggYnefoswegzD
VMware Eaxm 2V0-21.19
https://www.vmware.com/education-services/certification/vcp6-7-dcv-exam.html
The Professional vSphere 6.7 Exam validates that an individual can implement, manage, and troubleshoot a vSphere V6.7 infrastructure, using best practices to provide a powerful, flexible, and secure foundation for business agility that can accelerate the transformation to cloud computing.
Pass 2V0-21.19 Exam | Real Questions & Answers
QUESTION 1
A vSphere administrator configures log forwarding for remote syslog server in a vCenter Server Appliance (VCSA)
through the vCenter Server Appliance Management Interface (VAMI). What is the maximum number of remote syslog
servers that can be configured?
A. 1
B. 2
C. 3
D. 4
Correct Answer: C
Reference: https://docs.vmware.com/en/VMwarevSphere/6.7/com.vmware.vsphere.vcsa.doc/GUID-9633A961-A5C3-4658-B099-B81E0512DC21.html
QUESTION 2
An administrator configures vSphere Replication for a DR site.
Which two items should be deployed at the second site? (Choose two.)
A. array-based storage
B. vSphere Replication appliance
C. vCenter Server
D. vSphere Distributed Switch (VDS)
E. vSphere Data Protection (VDP)
Correct Answer: BC
QUESTION 3
A new AD domain has just been added to vSphere as an identity source. This new domain has a user group called
administrators group. Which role do the administrators group users have by default, when authenticated to vCenter
Server?
A. Read Only
B. No Cryptography Administrator
C. Administrator
D. No Access
Correct Answer: C
QUESTION 4
An administrator is elevating the security posture of a vSphere environment after a recent data breach. All VMs will be
encrypted as part of this plan. Which additional component is required for the encryption?
A. KMS server
B. two-factor authentication
C. encrypted vSphere vMotion
D. vSAN encryption
Correct Answer: C
QUESTION 5
What are two components of a VM-Host affinity rule? (Choose two.)
A. Host Group
B. Cluster settings
C. VM restart priority
D. VM restart action
E. VM Group
Correct Answer: AE
Reference: https://pubs.vmware.com/vsphere-51/index.jsp?topic=%2Fcom.vmware.vsphere.resmgmt.doc%2FGUID-2FB90EF5-7733-4095-8B66-F10D6C57B820.html
More https://www.pass4itsure.com/2v0-21-19.html
VMware Eaxm 2V0-41.19
Pass 2V0-41.19 Exam | Real Questions & Answers
QUESTION 1
Which command is used to verify the application of Distributed Firewall Rules applied to a VM on a KVM transport
node?
A. esxcli network firewall get
B. esxcli network ip connection list
C. ovs-vsctl add-br br-int
D. ovs-appctl -t /var/run/openvswitch/nsxa-ctl dfw/rules
Correct Answer: D
Reference: https://docs.vmware.com/en/VMware-NSX-T-Data-Center/2.2/nsxt_22_troubleshoot/GUID-E7A7C5BEC23E-4E6A-8B73-F9DBB54AC5F1.html
QUESTION 2
Which CLI command would an administrator use to allow syslog on an ESXi transport node when using the esxcli
utility?
A. esxcli network firewall ruleset -e syslog
B. esxcli network firewall ruleset set -a -e false
C. esxcli network firewall ruleset set -r syslog -e true
D. esxcli network firewall ruleset set -r sysloq -e false
Correct Answer: C
Reference: https://docs.vmware.com/en/VMware-NSX-T-Data-Center/2.2/nsxt_22_troubleshoot.pdf
QUESTION 3
A customer is preparing to deploy VMware Kubernetes on an NSX-T Data Center. What is the minimum MTU size for
the UPLINK profile?
A. 1600
B. 1650
C. 1550
D. 1500
Correct Answer: A
QUESTION 4
What is VMware\\’s recommendation for the minimum MTU requirements when planning a NSX-T Data Center
deployment?
A. MTU should be set to 1550 or less across the data center network including inter-data center connections.
B. MTU should be set to 1500 or less only on inter-data center connections.
C. Configure Path MTU Discovery and rely on fragmentation.
D. MTU should be set to 1600 or greater across the data center network including inter-data center connections.
Correct Answer: D
QUESTION 5
What is the maximum supported ECMP paths in NSX-T 2.4 Data Center?
A. 6
B. 8
C. 9
D. 7
Correct Answer: B
A maximum of eight ECMP paths are supported.
Reference: https://docs.vmware.com/en/VMware-NSX-T-Data-Center/2.4/administration/GUID-443B6B0DF179-429E-83F3-E136038332E0.html
VMware Eaxm 3V0-624
https://www.vmware.com/education-services/certification/vcap6-5-dcv-design-exam.html
This exam tests a candidate’s ability to develop a design given a set of customer requirements, determine the functional requirements needed to create a logical design and architect a physical design using these elements.
Pass 3V0-624 Exam | Real Questions & Answers
QUESTION 1
A system architect is building a design that includes three vCenter Server Appliances with 20 to 25 ESXi hosts each.
The reliability of the environment is the top business priority because the company runs several applications that must
be highly available.
Which VMware solution provides the ability to centrally detect issues in the environment and resolve them?
A. Set up a log collection and analysis engine such as VMware Log Insight and point all components of the vSphere
environment to this engine.
B. Enable the deactivated VMware Log Browser Service to capture and search logs in the vSphere Web Client.
C. Use the new vSphere HTML5 client that provides multiple ways to detect and isolate issues in the environment.
D. Use the vCenter Server Support Assistant as an easy way to create log bundles, then transfer them to VMware
support for analysis and resolution.
Correct Answer: A
QUESTION 2
A ompany Is in the piocess of deploying a modern video news-streaming application.
1.
The application is capable of scaling (expanding and collapsing) its streaming nodes in the form of virtual machines,
based on demand.
2.
To host the application, the company decided to implement a new VMware cluster with vSphere 6.5.
3.
The company wants to understand Network-Aware DRS and its ability to enhance the streaming application
performance. How can Network-Aware DRS help in this scenario?
A. Network-Aware DRS is a new low-level feature that will work in the background with very limited visibility to the
administrator.
B. Network-Aware DRS will only make sure that the host has sufficient network resources along with compute resources
required by the virtual machine.
C. Network-Aware DRS will display the host network load distribution under the Manage Tab in the vSphere Web
Client.
D. Network-Aware DRS will balance network load the same way as it manages the CPU and memory load.
Correct Answer: D
QUESTION 3
A company has requested that vSphere Virtual Machine Encryption be included in a vSphere 6.5 deployment design to
meet the security requirements specified by its compliance team. Which three design considerations would apply in this
case? (Choose three.)
A. RDM virtual machine disk configurations are NOT supported.
B. Suspend/resume operations for an encrypted virtual machine are NOT supported.
C. OVF Export is NOT supported for an encrypted virtual machine.
D. Encryption performance is independent of CPU and storage speed.
E. Cloning of encrypted virtual machine is NOT supported.
Correct Answer: BDE
QUESTION 4
A number of factors determine how many physical adapters are needed in a host design. Whichof the following is not
one of them?
A. Virtual machine size
B. Amount of bandwidth required
C. Security requirements
D. Hardware fault tolerance
Correct Answer: A
QUESTION 5
The hardware operations team is planning to purchase new ESXi hosts for the upcoming budget year and is requesting
recommendations on the type of servers to purchase for a web application. The web application consists of hundreds of
small virtual machines (1 vCPU and 8GB of RAM) that are members of a software cluster.
The solution should have these abilities:
1.
recover from ESXi host hardware failures
2.
zero downtime for a limited number of critical virtual machines (VMs)
3.
migrate running VMs between ESXi hosts without interruption to the operating system
4.
perform these functions using VMware ESXi servers, vCenter Server, and high-speed network interfaces
What are the three functional requirements and their associated VMware technologies? (Choose three.)
A. automatic restarts of failed VMs (vSphere HA)
B. high speed network interfaces (vSphere Distributed Switches)
C. ability to migrate running VMs (vSphere vMotion)
D. fault tolerance for limited number of critical VMs (vSphere FT)
E. VMware ESXi Servers (vSphere Auto Deploy)
Correct Answer: ACD
More https://www.pass4itsure.com/3v0-624.html
VMware Eaxm 3V0-752
https://www.vmware.com/education-services/certification/vcap7-dtm-design-exam.html
This exam tests a candidate’s ability to design a Horizon 7.2 solution by validating product and technical knowledge as well as the ability to analyze, evaluate, and create solutions.
Pass 3V0-752 Exam | Real Questions & Answers
QUESTION 1
A security team is implementing VMware Identity Manager to have a central point for authentication to facilitate access
to its company\\’s applications. The team would like to have users to authenticate to VMware Identity Manager before
being able to connect to a Horizon View Desktop.
What can be done to ensure that users who try to authenticate to the Horizon View Connection brokers are forced to
first authenticate to VMware Identity Manager?
A. Create a SAML authenticator in Horizon View and set it to “Allowed.”
B. Configure View advanced authentication to “Allowed” on the Horizon View Connection broker and create a Kerberos
authenticator on VMware Identity Manager.
C. Configure View authentication to “Not Allowed” on the Horizon View Connection broker and create a Kerberos
authenticator on VMware Identity Manager.
D. Create a SAML authenticator in Horizon View and set it to “Required.”
Correct Answer: D
QUESTION 2
A VDI Architect wants to optimize Blast Extreme protocol between 400 Horizon Windows clients and agents on an
organization\\’s LAN. No GPO currently makes Horizon settings to these clients or agents. What GPO setting will
improve performance of these systems?
A. Enable H264
B. Disable UDP Protocol
C. Enable UDP Protocol
D. Disable H264
Correct Answer: B
QUESTION 3
An architect is deploying Horizon 7.0 on vSAN 6.2. The architect wants to take advantage of the erasure coding feature
to save disk space. Each host contains 4TB of capacity flash disk. The desktop base image has 2GB of RAM and a
40GB
C: drive. The cluster must support 200 concurrent users.
Which two configurations satisfy requirements? (Choose two.)
A. 4-host cluster, FTT=2
B. 5-host cluster, FTT=2
C. 6-host cluster, FTT=2
D. 3-host cluster, FTT=1
E. 4-host cluster, FTT=1
Correct Answer: CE
QUESTION 4
A company is implementing VMware Horizon View 7 solution. It has created four 500 linked-clone desktop pools to be
used by different departments and workers. The company\\’s VDI administrator noticed that Horizon View Composer is
showing in error state on the View Admin Web Console. During restart of the Composer service, the service failed to
start up again. A decision was made to migrate View Composer to a new server and preserve the linked-clone
information.
What three steps are requires for the migration? (Choose three.)
A. Install View Connection Server on the new machine.
B. Create a new SQL database
C. Migrate the RSA key constrainer.
D. Configure Horizon View Composer to point to the existing SQL database.
E. Install the VMware Horizon View Composer service.
Correct Answer: CDE
QUESTION 5
An architect is designing Active Directory (AD) permissions for a Horizon environment that will use pre-existing
computer accounts. The AD Security Team has restrictions about the use of service accounts. What two sets of
minimum permission are needed to delegate to an AD service account? (Choose two.)
A. Create Computer Objects, Delete Computer Objects
B. List Contents, Read All Properties
C. Read Permissions, Reset Password
D. Write Permissions, Change Password
Correct Answer: BC
Reference: https://pubs.vmware.com/view-51/index.jsp?topic=%2Fcom.vmware.view.administration.doc%2FGUIDED99E026-5D70-4ADF-B4BC-A64A3386E10C.html
More https://www.pass4itsure.com/3v0-752.html
VMware Eaxm 5V0-21.19
The Professional VMware vSphere 6.7(2V0-21.19) which leads to VMware Certified Professional –Data Center Virtualization 2020certification is a 70-item exam, with a passing score of 300 using ascaled scoring method. Candidates are gi ven 115 mi nutes to complete the exam.
Pass 5V0-21.19 Exam | Real Questions & Answers
QUESTION 1
In stretched clusters, what is a benefit of implementing a virtual witness rather than a physical witness?
A. Reduced vSphere licensing
B. Shared metadata between separate clusters
C. Increased vSAN datastore capacity
D. Increased compute for running VMs
Correct Answer: A
Reference: https://cormachogan.com/2015/09/11/a-closer-look-at-the-vsan-witness-appliance/
QUESTION 2
vCenter reports a number of vSAN network alarms on a 2-node vSAN Direct Connect cluster. The test pings show
irregularities in the ping results. Using vSAN Health service, which two checks should be used to identify the network
root cause? (Choose two.)
A. Physical disk operation health
B. Network latency
C. vSAN extended configuration
D. vSAN disk balance
E. vSAN basic unicast connectivity
Correct Answer: AB
Reference: https://vsan-essentials.gitbooks.io/vsan-6-2/content/chapter10.html
QUESTION 3
Which type of encryption is used for the data encryption key on the vSAN datastore?
A. TLS 1.1
B. TLS 1.2
C. AES-XTS 256
D. AES-XTS 128
Correct Answer: C
Reference: https://searchvmware.techtarget.com/tip/VSAN-Encryption-What-it-is-what-it-does-and-how-to-use-it
QUESTION 4
An administrator is planning to deploy a new vSAN cluster with these requirements: -Physical adapters will share
capacity among several traffic types -Guaranteed bandwidth for vSAN during bandwidth contention -Enhanced security
and performance
What must be considered when configuring the new vSAN cluster?
A. Isolate traffic in a VLAN and utilize Network I/O Control
B. Utilize IOPS Limit rules in storage policies
C. Utilize jumbo frames with Network I/O Control
D. Implement vSphere I/O filters
Correct Answer: A
Reference: https://docs.vmware.com/en/VMware-vSphere/6.7/com.vmware.vsphere.vsanplanning.doc/GUID-031F9637-EE29-4684-8644-7A93B9FD8D7B.html
QUESTION 5
Where are the performance metrics for Write Buffer Free percentage located?
A. host level vSAN performance metrics
B. vSAN capacity graphs
C. vSAN Health Check
D. cluster level vSAN performance metrics
Correct Answer: D
Reference: https://docs.vmware.com/en/vRealize-OperationsManager/8.0/com.vmware.vcom.core.doc/GUID-97A69368-F085-451B-A53C-2210C1554A9D.html
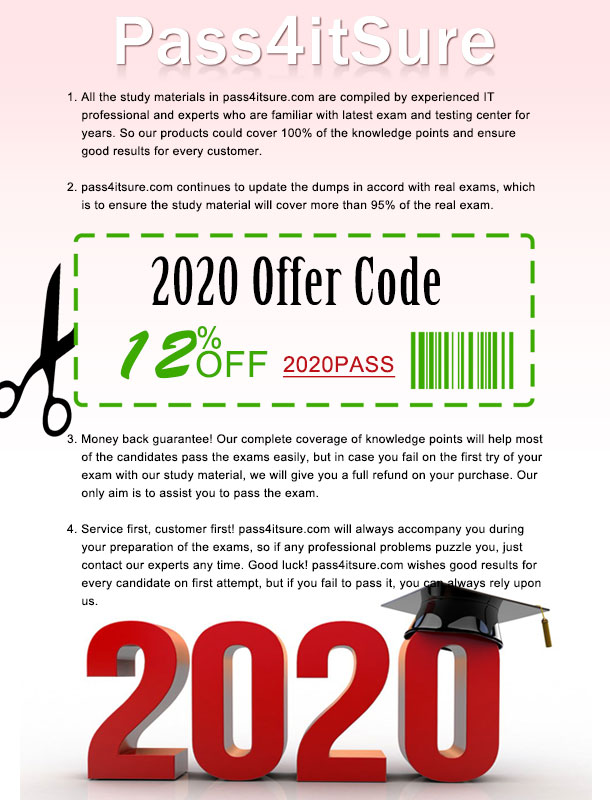
Pass4itsure discount code 2020
- Download VMware 2V0-21.19 Exam PDF Dumps https://drive.google.com/open?id=1YIIK99ErOg-sWut8CpSDlvPLViJRXq0z
- Download VMware 2V0-41.19 Exam PDF Dumps https://drive.google.com/open?id=15OVNOX-4aLX8qJuvLhvo98SYR58sjjGs
- Download VMware 3V0-624 Exam PDF Dumps https://drive.google.com/open?id=1PnEplZLRf8m_9Tz-ohzSiH9iW616Lfn7
- Download VMware 3V0-752 Exam PDF Dumps https://drive.google.com/open?id=1T4Yzzeb0rA7SYuRg088XRsF7gD1xS2y_
- Download VMware 5V0-21.19 Exam PDF Dumps https://drive.google.com/open?id=1BkJENokCYD5FkYVqazpggYnefoswegzD
https://www.pass4itsure.com/vmware.html is great source of vmware certification real exam questions with free 2V0-21.19,2V0-41.19,3V0-624,3V0-752,5V0-21.19 practice test questions and braindumps,video.